Q.E.D Is Fast Approaching
We are getting excited around here for the first ever QSA Educational Discussion! This is going to be a great event to hone your PCI compliance skills, get answers to those complex compliance questions and PCI DSS interpretations.
I Have Vulnerabilities On My LAN. So What?!
During the course of my penetration testing engagements (where I pretend I'm a malicious user and attempt to do naughty things on the network), I usually see or detect many vulnerabilities that are typically not found on the public internet. These vulnerabilities range from a small information disclosure (yawn) to full remote code execution (OH YES!) and of course everything in between. As a good security professional, my recommendations are to fix every single vulnerability found. This would exclude vulns that exist due to a specific business need, such as legacy systems or applications, or other legitimate reasons. When I suggest that we fix all of them, I often receive pushback from IT staff and sometimes even the stakeholders.
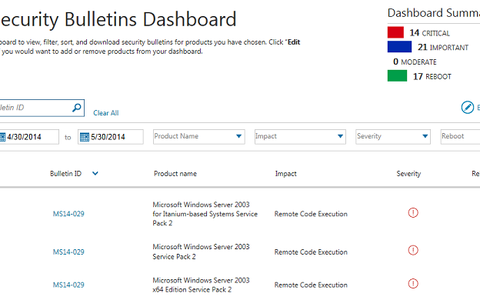
Microsoft My Bulletins & PCI Compliance
Microsoft just released a new tool for their Security TechCenter. Its a pretty straight-forward service called My Bulletins [^1]. Basically it provides a customized dashboard to present Microsoft security bulletins. The nice thing is that you can customize the dashboard to only receive notices for those Microsoft products you use and care about.
Heartbleed Hanging On
More than a month has past since the disclosure of the Heartbleed vulnerability and it is still making the rounds in the news. Even though it presents a serious security issue to Internet communication there are still a good number of servers and services that haven't been fixed. There is also evidence that a good portion of remediation efforts have fallen short and are insufficient to protect against and resolve the issues created by Heartbleed.
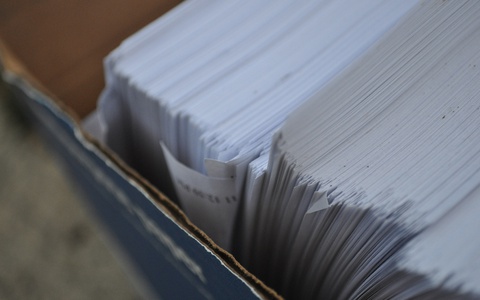
PCI Policy Documentation
Without fail, the first time an organization goes through the PCI gap assessment, remediation, and assessment cycle, they always underestimate the amount of specificity required by the PCI DSS. Smaller companies will spend a significant amount of time drafting and adopting new policies within their organization, while larger companies will spend their time trying to find which existing policies satisfy which requirements, making adjustments as necessary.